Obsidian Threat Heat Map
Having a way to track your incidents is pretty important. Imagine not having data analytics to derive threat models and predict risk... I'm not going to reinvent the wheel here, because things like Maltego exist, but I'm not really inventing anything here... this is just repurposing something I already utilize. Did you know you can use Obsidian to create your own "threat model"? **No data was harmed in the production of this experience, and all of it is fake data**. i.e. 8[.]8.8[.]8, 192[.]168[.]1[.]7 and johnny[.]smithapples[at]gmail[.]com.
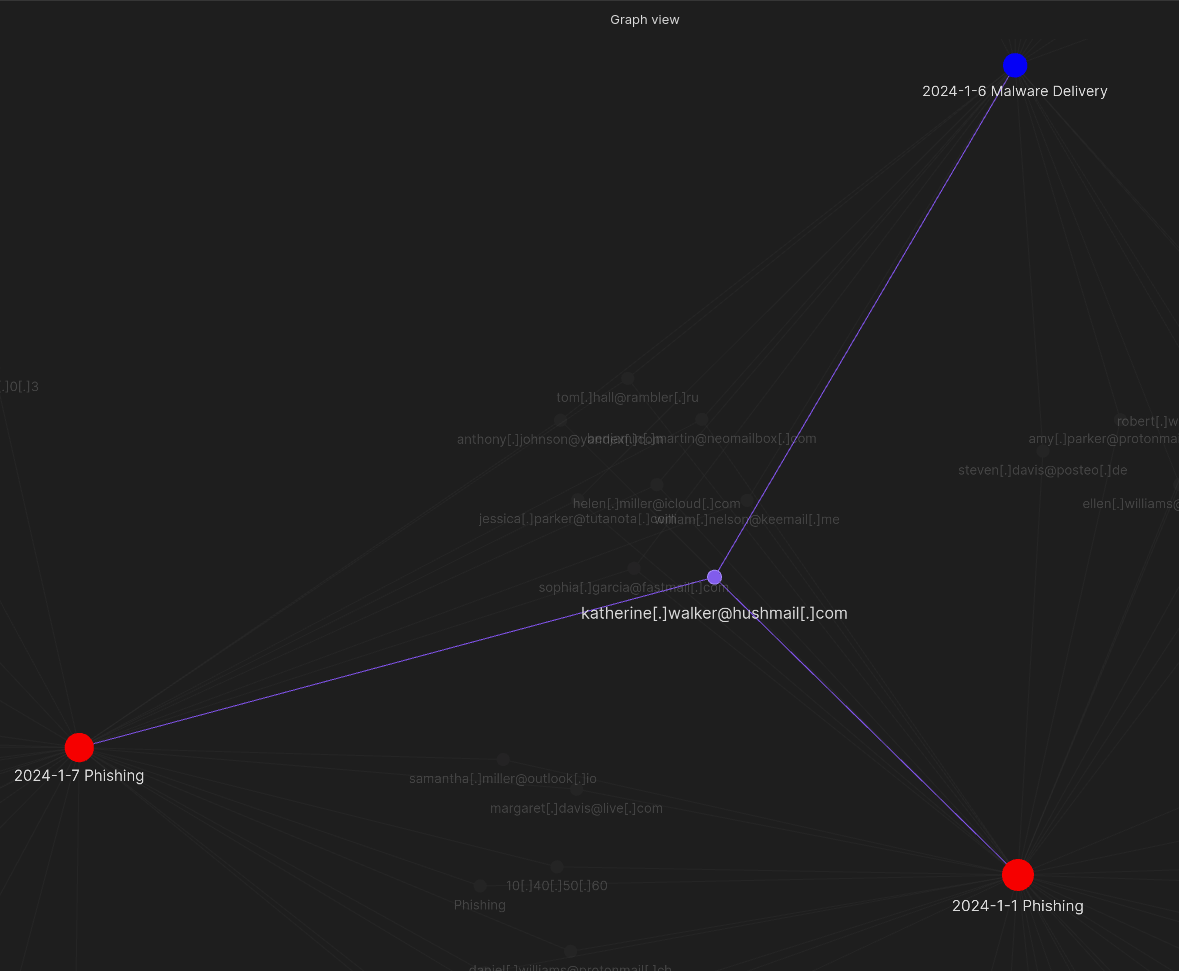 **Image 1: A beautiful heatmap in Obsidian**
**Image 1: A beautiful heatmap in Obsidian**
Obsidian.md is a Markdown reader/editor with the ability to create mind maps and do some note taking in some cool ways. I mostly used it for code notes and configs...until today. Let's put this together.
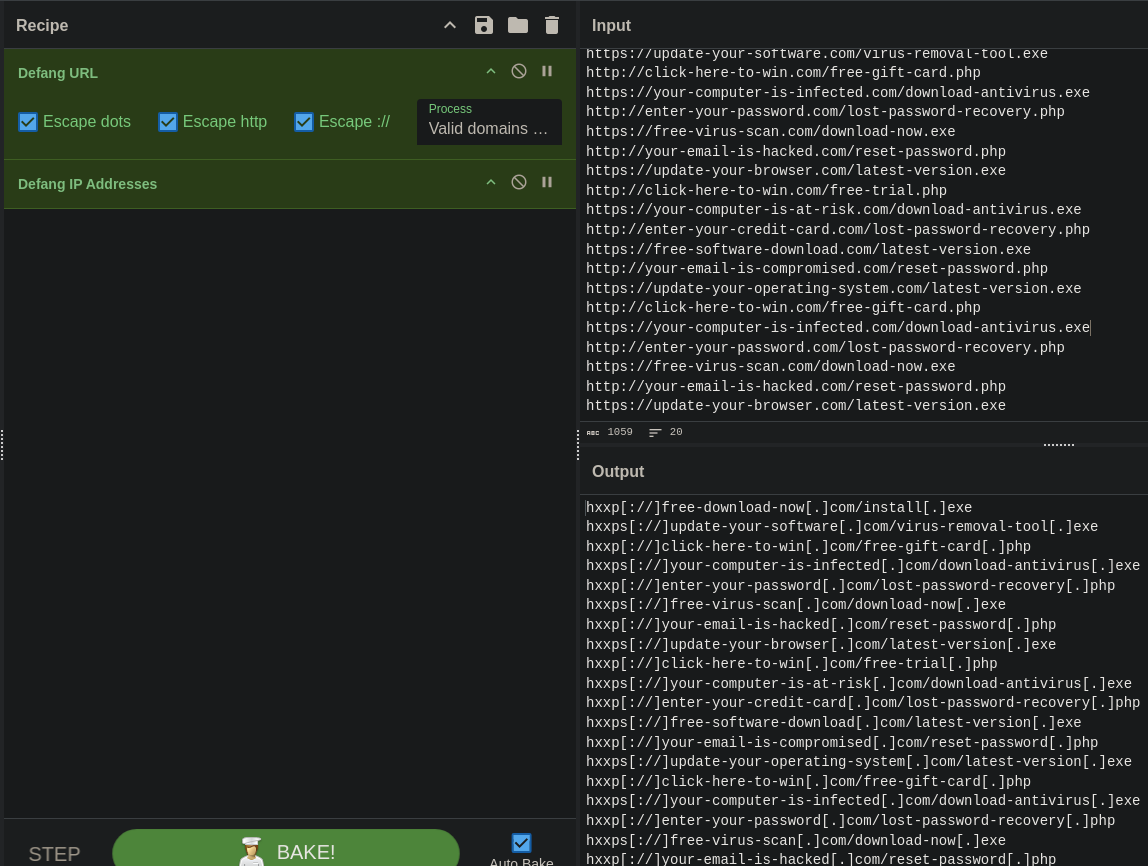 **Image 2: Defanging our Fake IOCs**
**Image 2: Defanging our Fake IOCs**
Firstly, throw IPs, URLs, Domains, Sender Addresses, Recipient Address, File Names, etc. through CyberChef or some other qualifying tool which can de-weaponize IOCs.
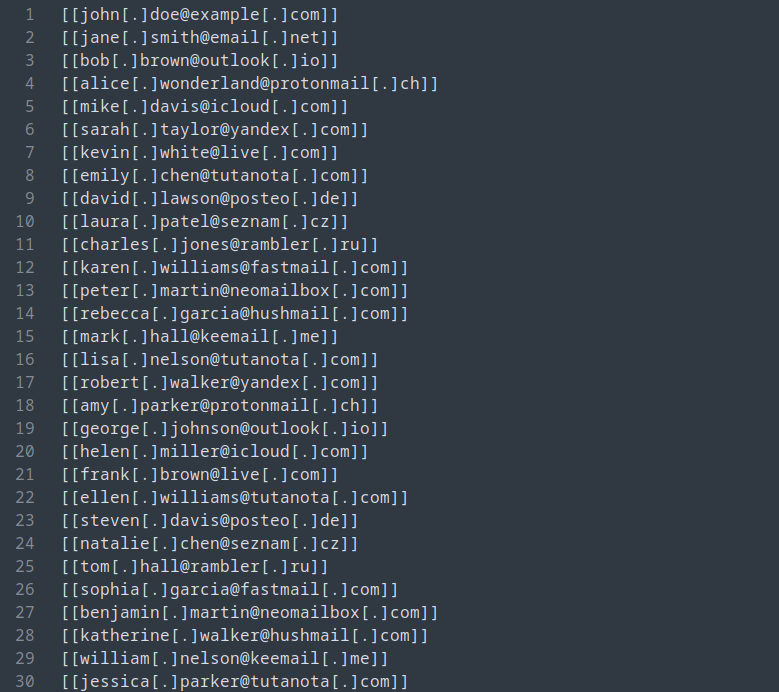 **Image 3: Performing Mass Text Manipulation**
**Image 3: Performing Mass Text Manipulation**
Next, with raw, defanged IOCs, move to a text editor like sublime (or VI, idk, you pick). Then, (sublime instructions), "Ctrl + A", "Ctrl + Shift + L", "Home" key, "Shift + End" keys, "[[". Done. Tagged. Wrapping text in Obsidian with [[YOUR TEXT]] creates a link, which shows up as a "dot" in Obsidian.
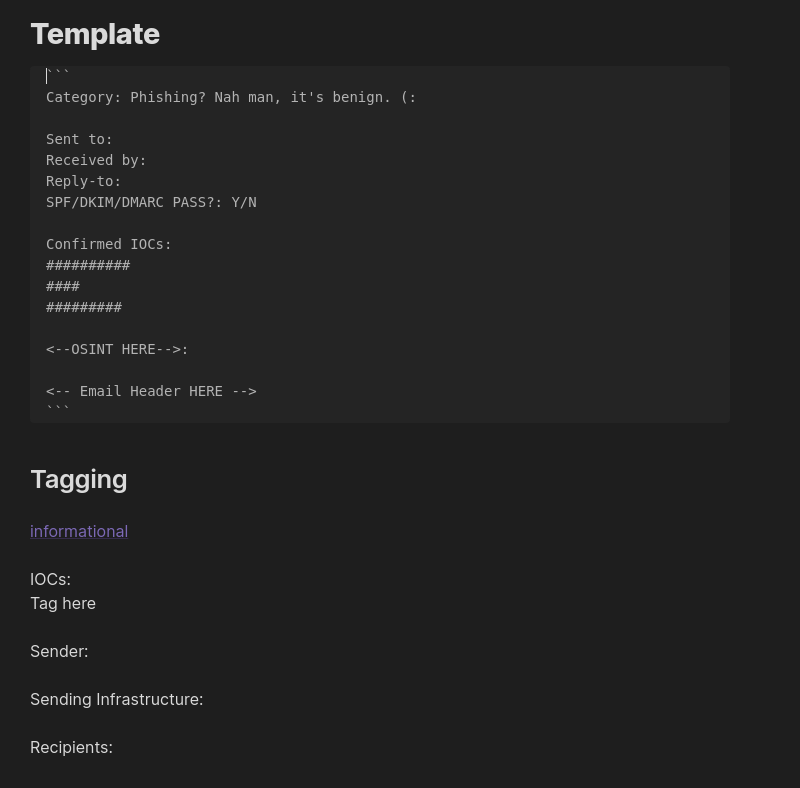 **Image 4: Template Incident Report**
**Image 4: Template Incident Report**
Once your data is prepared, translate your reports over to Obsidian with a template like this.
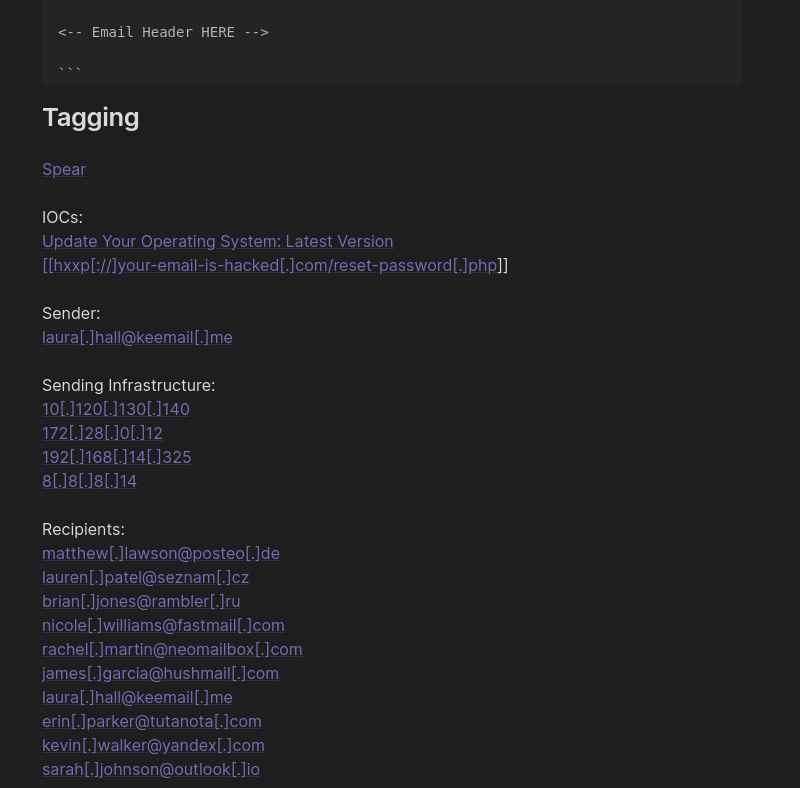 **Image 5: Loading our IOCs, tagged and defanged**
**Image 5: Loading our IOCs, tagged and defanged**
From here, you can see that "tagging" creates something similar to a link, but this is all done within Obsidian. Now, if you create two incident reports that happen to share an IOC or other tagged artifact, they will "link" together in "Graph View". It's almost so simple, it's genius.
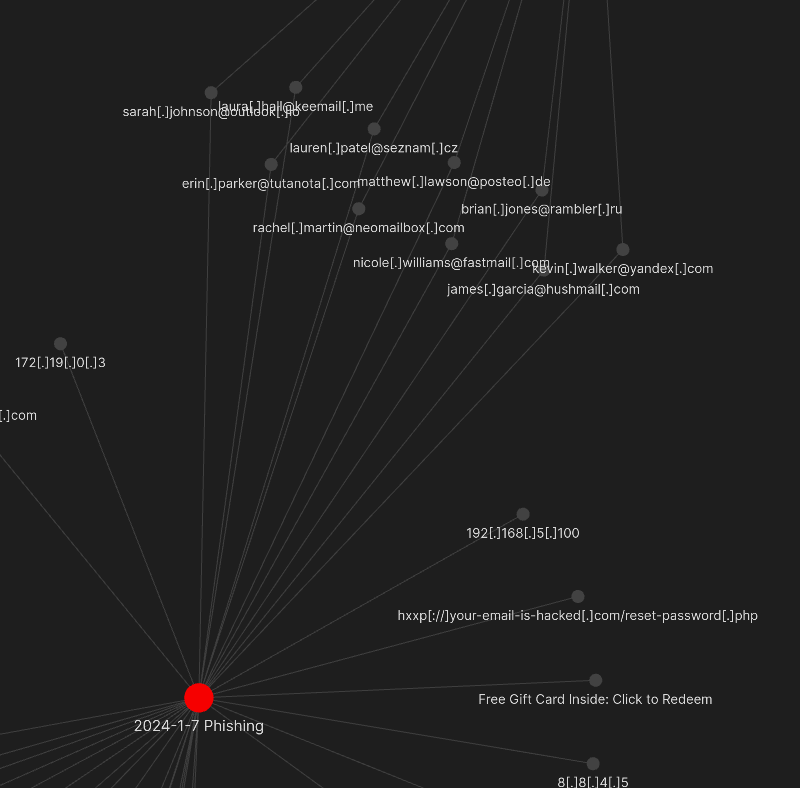 **Image 6: Observing our links**
**Image 6: Observing our links**
As you can imagine, over time, this will tend to generate VALUABLE data... for example, if you're sticking within the purview (ha) of emails, you can determine which groups of recipients are most at-risk. Obsidian also allows for you to string match, and group (creates another link), which can allow you to broadly classify types of incidents (i.e. whaling, qishing, spear-phishing, ???), and you can also tag "departments" filling out "Title" and "Department" information, which will of course... link together. At the high-level, this is a solution that can help you demonstrate the evolution of threats, as well as any that may be related. Mostly, this can help identify if specific areas need improvement, such as visually demonstrating at-risk users in a visually appealing way. Opportunities are endless here; you could also throw in host data/compromise information. Again; endless opportunities here.